 OK I’ll try my best to follow Cesar, this years keynote speaker, Francisco, one of the founders of EkoParty and Jennifer our CEO in giving an impression of the EkoParty conference. If you haven’t been to EkoParty, stop what you’re doing right now, check out the web site (http://ekoparty.org) and set yourself a reminder to buy a plane ticket and a entry ticket for next year – because this is a con worth attending. If nothing else you’ll learn or confirm what you had thought for years: that the Latin American hacker community is awesome and you should be paying attention to their research if you haven’t been already.
OK I’ll try my best to follow Cesar, this years keynote speaker, Francisco, one of the founders of EkoParty and Jennifer our CEO in giving an impression of the EkoParty conference. If you haven’t been to EkoParty, stop what you’re doing right now, check out the web site (http://ekoparty.org) and set yourself a reminder to buy a plane ticket and a entry ticket for next year – because this is a con worth attending. If nothing else you’ll learn or confirm what you had thought for years: that the Latin American hacker community is awesome and you should be paying attention to their research if you haven’t been already.
Three days long, EkoParty is compromised of a CTF, Lock picking area, training, and 20 interesting talks on research and security findings. The venue is something you’d expect from CCC or PH-Neutral: An Industrial, bare-bones building loaded up with ping pong tables and massive computing power with no shortness of smoke machines, lights and crazy gadgets on stage…oh and as you read above in Francisco’s summary, a Mariachi band (hey, it is Argentina!).
The building reminded me of the the elaborate Farady cage Gene Hackman had set up in the movie Enemy of the State that was used to hide from the CIA. Except Eko Party was filled with around 1500 attendees and organizers.
IOActive sponsored a a booth and tried their best to provide the attendees with as much quality alcohol as possible =]
Our booth is where I spent most of my time when not seeing talks, so that I could hang out with IOActive’s Latin American team members originating from Mexico, Brazil, Colombia and Argentina.
I saw a number of talks while at EkoParty, but I’m sure most of you will agree the three most noteworthy talks were:
-
- CRIME (Juliano Rizzo and Thai Doung)
-
- Cryptographic Flaws in Oracle Database Authentication Protocol (Esteban Fayo)
-
- Dirty use of USSD Codes in Cellular Network (Ravi Borgaonkar)
I won’t go into details on the above talks, as more information is now available online about them.
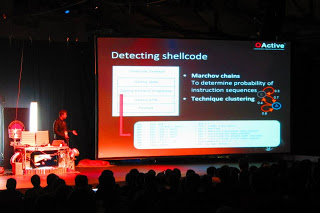
I was lucky enough to be accepted as as speaker this year and talk on research focused around defeating network and file-system detection. My past development experience is on detection of threats, but as I stated in my presentation: You must think offensively when creating defensive technology and make no mistake of overselling it’s limitations – a problem most salespeople at security companies have these days.
I spent about 75% of my time reviewing various content detection technologies from the last 20 years and explaining each one of their limitations. I then talked about the use of machine learning and natural language processing for both exploit and malware detection as well as attribution.
Machine learning like any technology used in defense, has it’s limitations and I tried to explain my point of view and importance of not only having a layered defense, but having a well thought out layered defense that makes sense for your organization.
As I stated in my presentation, attackers have several stages they typically go through to pull off a full attack and successfully ex-filtration data:
-
- Recon (Intelligence gathering)
-
- Penetration (exploitation of defenses)
-
- Control (staging a persistent mechanism within the network)
In my presentation I looked at the reality in offensive techniques against detection technologies: Attackers are going to stay just enough ahead of the defense curve to avoid detection.
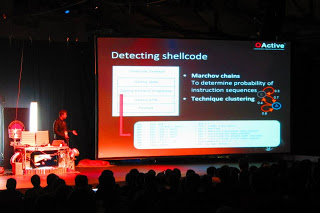 |
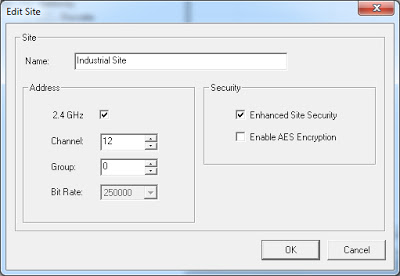
(Stephan Chenette’s presentation on
“the Future of Automated Malware Generation”) |
For example with Gauss and Zeus we’ve seen dlls being encrypted with a key only found on the targeted machine and downloaded binaries encrypted with information from the infected host – FYI – encrypting binaries with target information basically kills the possibility of any behavior sandbox from being able to run the binary outside of it’s intended environment.
So maybe attackers of the future will only make incremental improvements to thwart detection OR maybe we’ll start seeing anti-clustering and anti-classifications added to the attacker’s arsenal as machine learning is added as another layer of defense – The future is of course unknown – but I do have my suspicions.
In my concluding slides I stressed that there is much improvement that can be made on the side of detecting the threat before it happens as well as making sure that a defensive strategy should be layered in a manor that focuses on making the attacker spend, time, resources and different skill levels at each layer, hopefully comprising enough of his or herself in the process and giving the targeted organization enough time to mitigate the threat if not halt the attack all together.
This was by far the largest crowd I’ve ever spoken in front of and goes down as one of the best conferences I’ve attended. Thanks again EkoParty committee for inviting me to present, I’ll try my best to be back next year!!
By Ariel Sanchez
We had the opportunity at the Ekoparty to attend presentations which a show high level of innovation and creativity.
Here are some personal highlights:
*The CRIME Attack presentation by Juliano Rizzo and Thai Doung
*Trace Surfing presentation by Agustin Gianni
*Cryptographic flaws in Oracle Database authentication protocol presentation by Esteban Fayo
I can’t wait to see what is coming in the next ekoparty!
If my memory is accurate, this was my fourth EkoParty. From the first time to now, the numbers related to the conference have grown beyond my imagination. On the other hand, EkoParty remains the same on another aspect: it has the energetic blood of Latin American hackers. Too many of them, actually. Buenos Aires has a magical history of popping up talents like nowhere else. And the impressive numbers and quality of EkoParty, today, definitely have to do with that magic.
There were many great talks, on a wide range of topics. I will summarize the ones I mostly appreciated, being forced to leave aside the ones I didn’t have the chance to catch.
Cyberwar para todos, I’ve seen people complaining about this topic, either because it’s political (rather than technical), or because “it’s been too stressed” already. In my opinion, one can’t ignore how the big empires think of information security. Specifically, here is what I liked about this talk: the topic might have been stressed in North America, but the notion of cyberwar, per Gen. Keith Alexander’s vision, is still unknown to most in South America. A few years ago, the Brazilian CDCiber (Cyber Defense Centre) was created and, despite effort coming directly from the President, the local authorities are still very naïve, to say least, if compared to their rich cousins. Cesar raises questions about that.
Satellite baseband mods: Taking control of the InmarSat GMR-2 phone terminal, this was probably my favorite talk. They showed how a user can easily modify satellite phones at will, poking data that comes in and out of the device. Furthermore, the presenters showed how communication technologies very similar to GSM, when applied over a different medium, can open whole new vectors of potential attacks. Finally, Sebastian “Topo” Muniz is one of the most hilarious speakers in the infosec industry.
Trace Surfing, this is one of those rare talks that resolve hard problems with very simple solutions. Agustín showed how one can retrieve high-level information about the Windows heap, during the course of an execution trace, simply by tracking ABI specifics at call-sites of choice. The simplicity of his solution also makes it really fast. Great work!
PIN para todos (y todas), basically Pablo Sole created an interface that allows one to write Pin-based tools to instrument JavaScript. I heard it’s impressively fast.
What I really wanted to have seen, but couldn’t…
OPSEC: Because Jail is for wuftpd, unfortunately, they had Grugq speaking at 9am. I can’t digest humour so early and will have to ask him for a secondhand presentation.
Literacy for Integrated Circuit Reverse Engineering, very sadly, I didn’t catch Alex’s presentation. But if you are into reverse engineering modern devices, I would recommend it with both my eyes closed, nonetheless.
By Lucas Apa @lucasapa
What begun publicly as an e-zine in the early century now arises as the most important latin american security conference “ekoparty”. All the latin american team landed Buenos Aires to spend an amazing week.
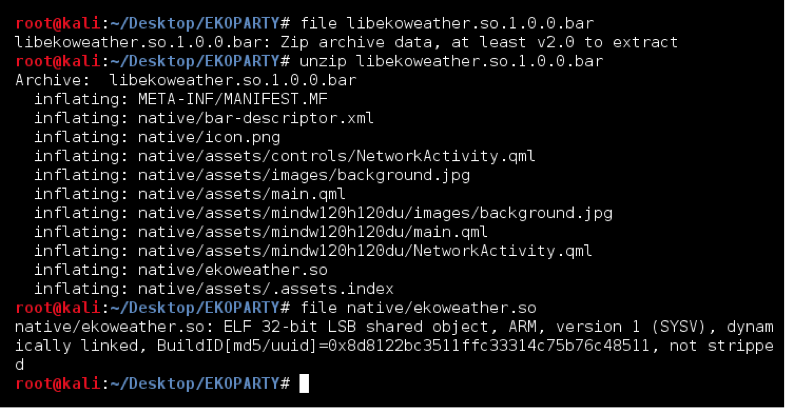
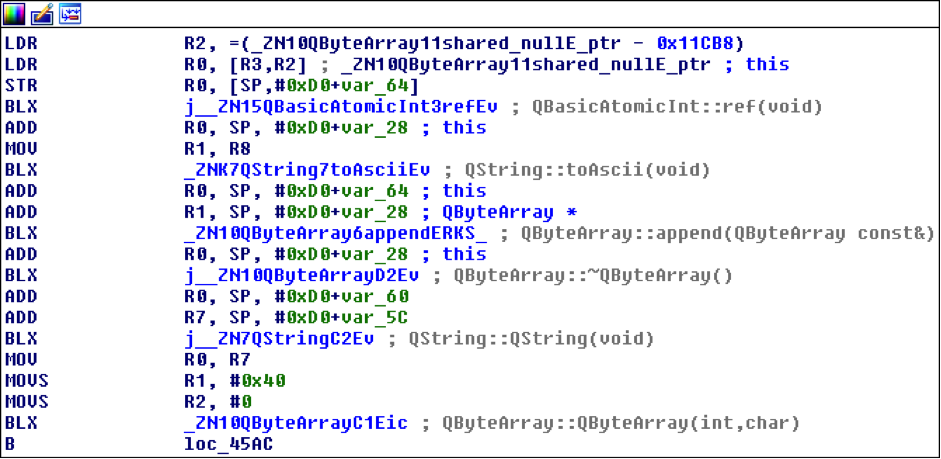
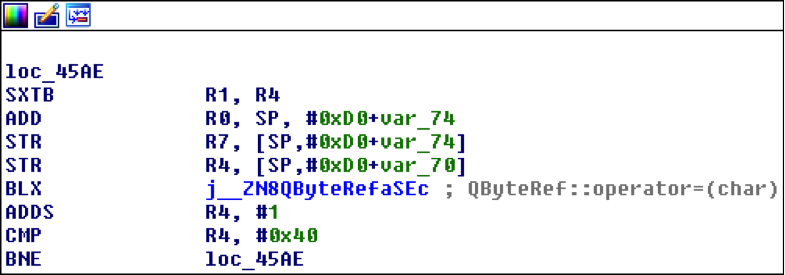
My “ekoparty week” started on monday where I got invited to attend a “Malware Analysis Training” by ESET after solving a challenge of “binary unpacking” posted on their blog. First, two intensive days were held with paid trainings which covered the following topics: cracking, exploiting, sap security, penetration testing, web security, digital forensics and threats defense. Every classroom was almost fully booked.
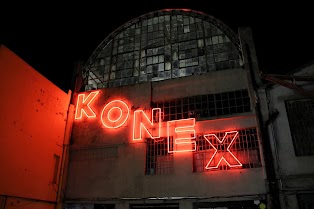
The conference started on Wednesday in “Konex Cultural Center”, one of the most famous cultural centers especially for music and events. The building used to be an oil factory some decades ago.
On Wednesday, our CTO Cesar Cerrudo, was the main keynote of the day.
Many workshops were open for any conference assistant for the rest of the day.
At night we enjoyed a classic “Mexican Grill” at IOActive’s party where VIP guests were invited. The meal was brought you by Alejandro Hernández and Diego Madero, our Mexican Security Consultants.
On Thursday and Friday were the most awaited days since the presentations were going to start.
My favorite talks were:
*Taking control of the InmarSat GMR-2 phone terminal (Sebastian Muñiz and Alfredo Ortega): Without modifying the firmware image, researchers managed to send AT commands to the phone terminal to write arbitrary memory. They copied binary instrumentation code for logging and hooking what really sends the phone on common actions like sending SMS. Then, they wrote the “data” section for redirecting the flow at some point and discovered that messages sent to the satellite “might” be vulnerable to
“memory corruption” if they are preprocessed by the satellite before retransmision. No satellites were harmed.
*VGA Persistent Rootkit (Nicolás Economou and Diego Juarez): Showed a new combo of techniques for modifing reliably the firmware of a VGA card to execute code or add new malicious basic blocks.
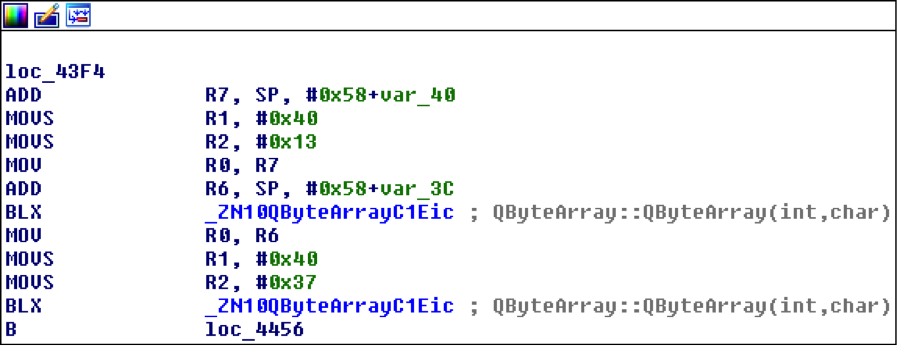
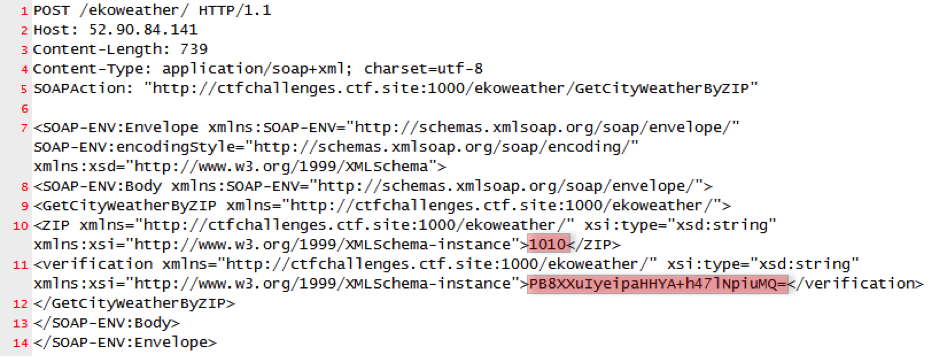
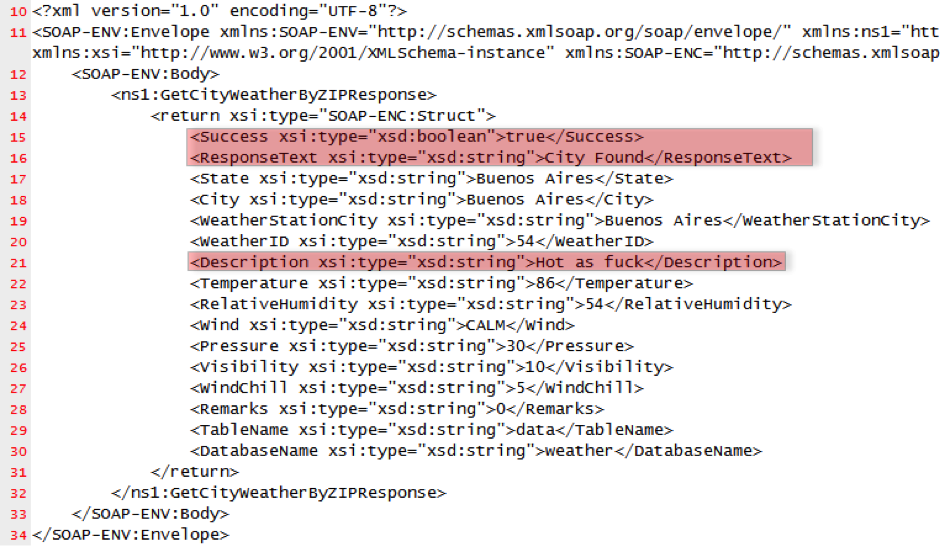
*The Crime (Juliano Rizzo and Thai Duong): The most awaited talk revealed a new chosen plaintext attack where compression allowed to recognize which secuences of bytes were already on the TLS data. The attack works like BEAST, with two requirements: capture encrypted victim’s traffic and control his browser by using a web vulnerability (or MITM on an HTTP service). When forcing the browser to issuing some specific words on the HTTP resource location, they figured that if that portion of the random string is already on the cookie the TLS data gets more compressed. This allows to bruteforce to identify the piggybacked cookie that is automatically added to the request.
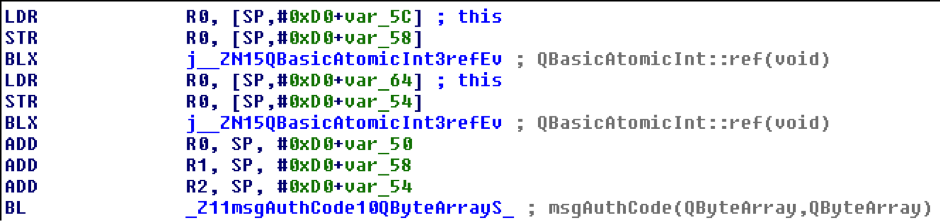
*The Future of Automated Malware Generation (Stephan Chenette): Our Director of R&D showed how different AV’s performs approaches for detecting malware mostly failing. It is difficult to defend ourselves in something we dont know but we must remember that attackers are also having fun with Machine Learning too !
*Cryptographic flaws in Oracle DB auth protocol (Esteban Fayó): When authenticating a user, Oracle uses the hashed password (on the database) as the key for encrypting the server session (random). The user hashes its password and then tries to decrypt the encrypted session that the server returned. The problem is that is possible to recognize if this decryption returns an invalid padding so the initial password can be tried offline. This allows to bruteforce the process of decrypting locally till a valid padding occurs (sometimes it colides with a valid padding but it’s not actually the password). This vulnerability was
reported to Oracle 2 years ago but no patch was provided by them till then.
After a 10 hours delayed flight, finally I landed to Buenos Aires. As soon as I could, I went straight to the VIP party to meet with the IOActive team and to prepare some mexican tacos and quesadillas (made by Diego Bauche @dexosexo).
The next day, Thursday, I had the chance to be at the Stephan Chanette’s talk (@StephanChenette), which was a really interesting presentation about automated malware generation and future expectations. His presentation had a good structure because he started with the current state of malware generation/defense and later he explained the future of malware generation/defense passing through the actual malware trends. The same day, I enjoyed the Esteban Fayo’s talk (@estemf) because he showed a live demo on how to crack an Oracle password taking advantage of some flaws in the Oracle authentication protocol.
The venue, KONEX, the same as the last year, was really cool, there were vendors booths, old computers, video games (where I spent like two hours playing Super Mario Bros) as well as a cocktail bar, obviously the IOActive booth ;).
In conclusion, I really had a great time with my fellow workers, drinking red wine and argentine asado, besides amazing conferences.
Definitely, I hope to be there the next year.