We are excited to announce that IOActive received multiple prestigious awards wins this year! Keep this blog bookmarked to always stay up-to-date on the company’s accomplishments throughout 2024.
Last updated September 30, 2024

IOActive was honored for its ability to maximize security investments and enhance clients’ overall security posture and business resilience. Unlike many organizations that default to defensive strategies, we at IOActive go beyond standard penetration testing to provide clients with red and purple team services that exceed typical assessments. We prioritize a comprehensive understanding of cyber adversaries through custom adversary emulation and ethical real-world attack simulations to develop robust, secure frameworks.
“We’re delighted to win awards in multiple categories throughout 2024,” said Jennifer Sunshine Steffens, CEO at IOActive. “These awards emphasize our nearly 30 years of leadership providing unique ‘attacker’s perspective’ methodologies that drive our research-fueled approach to security services trusted by Fortune 1000 companies worldwide.”
IOActive sets itself apart from the competition by bringing a unique attacker’s perspective to every client engagement, in order to maximize security investments and improve client’s overall security posture and business resiliency.
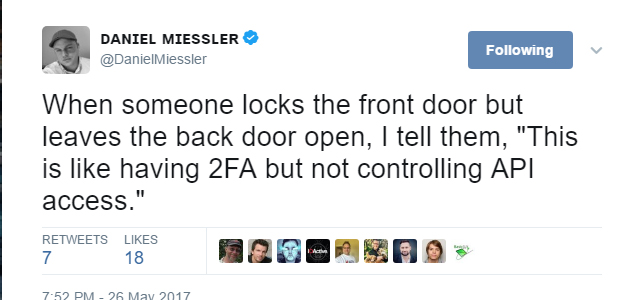
While many organizations focus on defense by ‘default,’ IOActive’s approach encourages secure-by-design practices and policies by introducing businesses to an attacker’s mindset so that they can better understand the threat landscape.
Understanding our adversaries is crucial. Therefore, our penetration teams surpass standard penetration testing to offer our clients a range of red and blue team solutions that go beyond traditional approaches.
Check out our secured awards below:
2024 Corporate Excellence Awards
Best Research-Led Security Services Provider 2024 – USA
IOActive is a proud winner of this year’s ‘Best Research-Led Security Services Provider 2024 – USA’ through the implementation of up-to-date research embedded in the delivery of services. The Corporate Excellence Awards ‘showcase the companies and individuals that are committed to innovation, business growth, and providing the very best products and services to clients across a wide range of industries.’

2024 Cyber Security Excellence Awards
Pen Test Team of the Year
IOActive’s penetration testing team sets itself apart from the competition by bringing a unique attacker’s perspective to every client engagement in order to maximize security investments and improve client’s overall security posture and business resiliency.

Cybersecurity Team of the Year
At IOActive, our team provides more than traditional penetration testing. We freely share our security expertise through a range of offerings including red and purple team exercises, attack simulations, security consultancy, and our highly specialized technical and programmatic services.

In addition, our leaders and consultants, spearheaded by CEO Jennifer Sunshine Steffens, have
served long tenures in the cybersecurity field and are highly skilled in research, strategic security services, risk management, quality assurance, and regulatory requirements.
Cybersecurity Provider of the Year
IOActive is a worldwide leader in research-fueled security services implementing unique “attacker’s perspective” methodologies that form the foundation of the company’s global service offerings.
Whether our customers need guidance, on-the-ground penetration testing, or the assistance of a virtual CISO, we are committed to assuring client satisfaction.

We constantly strive to develop new ways to assist our customers in handling today’s complex threatscape and long component lifecycles. Every client engagement is tailored to maximize security investments and improve overall security postures and business resiliency.
2024 Global Infosec Awards
Trailblazing Cybersecurity Service Provider
Our team has conducted groundbreaking research within a variety of industries, including research into the Boeing airplane’s network, uncovering vehicle vulnerabilities by hacking into a Jeep, a card shuffler machine and much more.
Our security services, spanning across the silicon and hardware-based levels to real-world attack simulations, demonstrate our expertise in ensuring organizations achieve security resilience.

Just as each cyberattacker and threat is different, we ensure our services are tailored to the needs of our clients – and we take pride in exceeding expectations, every time.
Trailblazing Cybersecurity Research
Our diverse cybersecurity team, with a presence in over 30 countries worldwide, combines decades of experience with cutting-edge research to develop innovative security solutions suitable for a broad range of industries and companies.

We count Fortune 1000 organizations among our customers, and we provide research-backed services across industries including automotive, medical devices, aviation, and satellite communications. Overall, we are deeply committed to offering unrelenting value and support internationally and to all of our customers.