Ransomware attacks have boomed during the last few years, becoming a preferred method for cybercriminals to get monetary profit by encrypting victim information and requiring a ransom to get the information back. The primary ransomware target has always been information. When a victim has no backup of that information, he panics, forced to pay for its return.
(more…)
Tag: cyberwarfare
WannaCry vs. Petya: Keys to Ransomware Effectiveness
With WannaCry and now Petya we’re beginning to see how and why the new strain of ransomware worms are evolving and growing far more effective than previous versions.
I think there are 3 main factors: Propagation, Payload, and Payment.*
- Propagation: You ideally want to be able to spread using as many different types of techniques as you can.
- Payload: Once you’ve infected the system you want to have a payload that encrypts properly, doesn’t have any easy bypass to decryption, and clearly indicates to the victim what they should do next.
- Payment: You need to be able to take in money efficiently and then actually decrypt the systems of those who pay. This piece is crucial, otherwise people will quickly learn they can’t get their files back even if they do pay and be inclined to just start over.
WannaCry vs. Petya
WannaCry used SMB as its main spreading mechanism, and its payment infrastructure lacked the ability to scale. It also had a kill switch, which was famously triggered and halted further propagation.
Petya on the other hand appears to be much more effective at spreading since it’s using both EternalBlue and credential sharing
/ PSEXEC to infect more systems. This means it can harvest working credentials and spread even if the new targets aren’t vulnerable to an exploit.
[NOTE: This is early analysis so some details could turn out to be different as we learn more.]
What remains to be seen is how effective the payload and payment infrastructures are on this one. It’s one thing to encrypt files, but it’s something else entirely to decrypt them.
The other important unknown at this point is if Petya is standalone or a component of a more elaborate attack. Is what we’re seeing now intended to be a compelling distraction?
There’s been some reports indicating these exploits were utilized by a sophisticated threat actor against the same targets prior to WannaCry. So it’s possible that WannaCry was poorly designed on purpose. Either way, we’re advising clients to investigate if there is any evidence of a more strategic use of these tools in the weeks leading up to Petya hitting.
*Note: I’m sure there are many more thorough ways to analyze the efficacy of worms. These are just three that came to mind while reading about Petya and thinking about it compared to WannaCry.
A Wake-up Call for SATCOM Security
- Aerospace
- Maritime
- Military and governments
- Emergency services
- Industrial (oil rigs, gas, electricity)
- Media
Practical and cheap cyberwar (cyber-warfare): Part II
|
Site
|
Accounts
|
%
|
|
Facebook
|
308
|
17.26457
|
|
Google
|
229
|
12.83632
|
|
Orbitz
|
182
|
10.20179
|
|
WashingtonPost
|
149
|
8.352018
|
|
Twitter
|
108
|
6.053812
|
|
Plaxo
|
93
|
5.213004
|
|
LinkedIn
|
65
|
3.643498
|
|
Garmin
|
45
|
2.522422
|
|
MySpace
|
44
|
2.466368
|
|
Dropbox
|
44
|
2.466368
|
|
NYTimes
|
36
|
2.017937
|
|
NikePlus
|
23
|
1.289238
|
|
Skype
|
16
|
0.896861
|
|
Hulu
|
13
|
0.7287
|
|
Economist
|
11
|
0.616592
|
|
Sony Entertainment Network
|
9
|
0.504484
|
|
Ask
|
3
|
0.168161
|
|
Gartner
|
3
|
0.168161
|
|
Travelers
|
2
|
0.112108
|
|
Naymz
|
2
|
0.112108
|
|
Posterous
|
1
|
0.056054
|


|
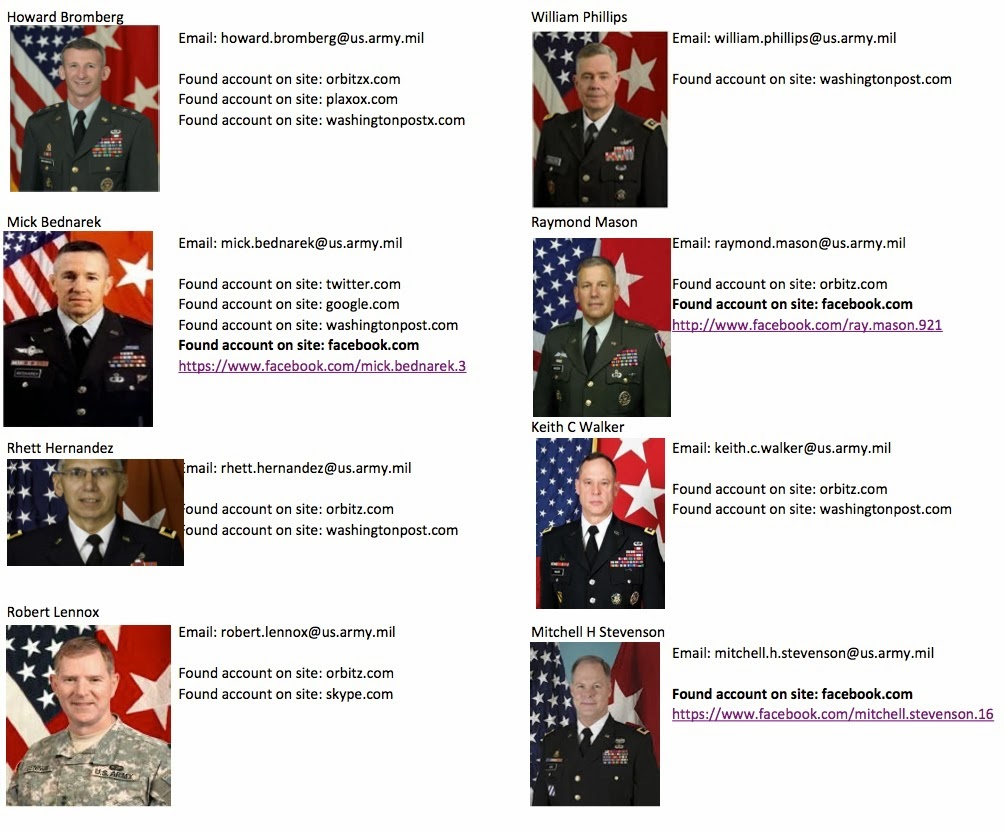
Robert Abrams
|
Email: robert.abrams@us.army.mil
|
|
|
|
|
|
Found account on site: orbitz.com
|
|
|
Found account on site: washingtonpost.com
|
|
|
|
|
Jamos Boozer
|
Email: james.boozer@us.army.mil
|
|
|
|
|
|
Found account on site: orbitz.com
|
|
|
Found account on site: facebook.com
|
|
|
|
|
Vincent Brooks
|
Email: vincent.brooks@us.army.mil
|
|
|
|
|
|
Found account on site: facebook.com
|
|
|
Found account on site: linkedin.com
|
|
|
|
|
James Eggleton
|
Email: james.eggleton@us.army.mil
|
|
|
|
|
|
Found account on site: plaxox.com
|
|
|
|
|
Reuben Jones
|
Email: reuben.jones@us.army.mil
|
|
|
|
|
|
Found account on site: plaxo.com
|
|
|
Found account on site: washingtonpost.com
|
|
|
|
|
|
|
|
David quantock
|
Email: david-quantock@us.army.mil
|
|
|
|
|
|
Found account on site: twitter.com
|
|
|
Found account on site: orbitz.com
|
|
|
Found account on site: plaxo.com
|
|
|
|
|
|
|
|
Dave Halverson
|
Email: dave.halverson@conus.army.mil
|
|
|
|
|
|
Found account on site: linkedin.com
|
|
|
|
|
Jo Bourque
|
Email: jo.bourque@us.army.mil
|
|
|
|
|
|
Found account on site: washingtonpost.com
|
|
|
|
|
|
|
|
Kev Leonard
|
Email: kev-leonard@us.army.mil
|
|
|
|
|
|
Found account on site: facebook.com
|
|
|
|
|
James Rogers
|
Email: james.rogers@us.army.mil
|
|
|
|
|
|
Found account on site: plaxo.com
|
|
|
|
|
|
|
|
William Crosby
|
Email: william.crosby@us.army.mil
|
|
|
|
|
|
Found account on site: linkedin.com
|
|
|
|
|
Anthony Cucolo
|
Email: anthony.cucolo@us.army.mil
|
|
|
|
|
|
Found account on site: twitter.com
|
|
|
Found account on site: orbitz.com
|
|
|
Found account on site: skype.com
|
|
|
Found account on site: plaxo.com
|
|
|
Found account on site: washingtonpost.com
|
|
|
Found account on site: linkedin.com
|
|
|
|
|
Genaro Dellrocco
|
Email: genaro.dellarocco@msl.army.mil
|
|
|
|
|
|
Found account on site: linkedin.com
|
|
|
|
|
Stephen Lanza
|
Email: stephen.lanza@us.army.mil
|
|
|
|
|
|
Found account on site: skype.com
|
|
|
Found account on site: plaxo.com
|
|
|
Found account on site: nytimes.com
|
|
|
|
|
Kurt Stein
|
Email: kurt-stein@us.army.mil
|
|
|
|
|
|
Found account on site: orbitz.com
|
|
|
Found account on site: skype.com
|
- Many have Facebook accounts exposing to public the family and friend relations that could be targeted by attackers.
- Most of them read and are probably subscribed to The Washington Post (makes sense, no?). This could be an interesting avenue for attacks such as phishing and watering hole attacks.
- Many of them use orbitz.com, probably for car rentals. Hacking this site can give attackers a lot of information about how they move, when they travel, etc.
- Many of them have accounts on google.com probably meaning they have Android devices (Smartphones, tablets, etc.).This could allow attackers to compromise the devices remotely (by email for instance) with known or 0days exploits since these devices are not usually patched and not very secure.
- And last but not least, many of them including Generals use garmin.com or nikeplus.com. Those websites are related with GPS devices including running watches. These websites allow you to upload GPS information making them very valuable for attackers for tracking purposes. They could know on what area a person usually runs, travel, etc.
Practical and cheap cyberwar (cyber-warfare): Part I
The idea of this post is to raise awareness. I want to show how vulnerable some industrial, oil, and gas installations currently are and how easy it is to attack them. Another goal is to pressure vendors to produce more secure devices and to speed up the patching process once vulnerabilities are reported.

