Introduction
In this blog post we compare the security and throughput performance of 5G cellular to that of WiFi. This work is part of the research IOActive published in a recent whitepaper (https://bit.ly/ioa-report-wifi-5g), which was commissioned by Dell. We used a Dell Latitude 7340 laptop as an end-user wireless device, a Panda Wireless® PAU06 as a WiFi access point, and an Ettus Research™ Universal Software Radio Peripheral (USRP™) B210 as a 5G base station to simulate a typical standalone 5G configuration and three typical WiFi network configurations (home, public, and corporate). Testing was performed between January and February 2024 during which we simulated a number of different attacks against these networks and measured performance-based results for a number of different real-world environments.
Security Tests
We researched known 5G and WiFi attacks and grouped them according to five different goals: user tracking, sensitive data interception, user impersonation, network impersonation, and denial of service. These goals easily map to the classic Confidentiality, Integrity, Availability (CIA) security triad. We then reproduced the attacks against our controlled test networks to better understand their requirements, characteristics, and impact. The results of these investigations are summarized below:
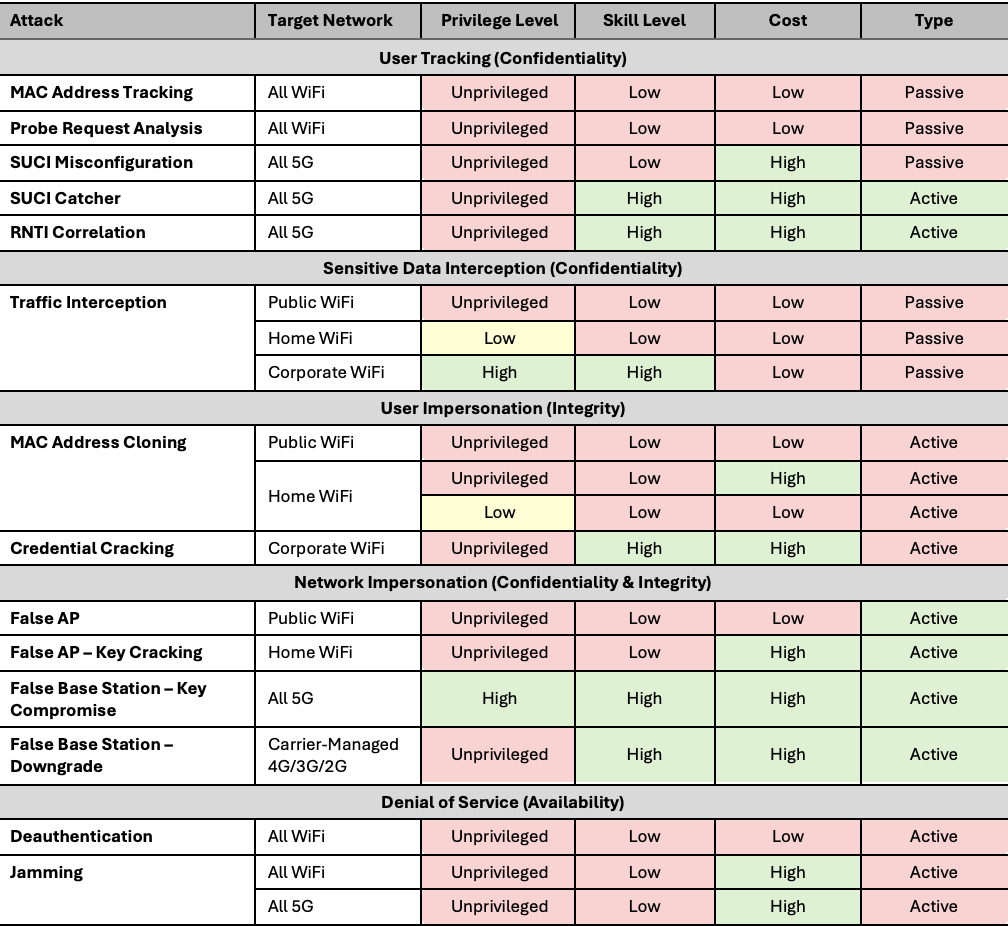
We noted that, in general, the 5G protocol was designed from the ground up to provide several assurances that the WiFi protocol does not provide. Although mitigations are available to address some of the attacks, WiFi is still unable to match the level of assurance provided by 5G.
For example, 5G protects against user tracking by using concealed identifiers. Attacks to bypass these identifiers are easily detectable and require highly skilled and well-funded attackers. In contrast, WiFi does not attempt to protect against user tracking, since MAC addresses are transmitted in plaintext with every packet. Although modern devices have tried to mitigate this risk by introducing MAC address randomization, passive user tracking is still easy to accomplish due to shortcomings in MAC address randomization and probe request analysis.
IOActive also noted that the use of layered security protocols mitigated most sensitive data interception and network impersonation attacks. Although the majority of users do not use a VPN when connecting to the Internet, most websites use TLS, which, when combined with HSTS and browser preload lists, effectively prevents an attacker from intercepting most of the sensitive data a user might access online. However, even multiple layered security protocols cannot protect against vulnerabilities in the underlying radio protocol. For example, a WiFi deauthentication attack would not be affected in any way by the use of TLS or a VPN.
Performance Tests
We conducted performance tests by measuring throughput and latency from a wireless device in a variety of environments, ranging from urban settings with high spectrum noise and many physical obstacles, to rural areas where measurements more closely reflected the attributes of the underlying radio protocol.
Of particular note, we found that a wireless device could maintain a connection to a 5G wireless base over a significant distance, even with substantial interference from buildings and other structures in an urban environment.
In a rural environment, our WiFi testing showed an exponential decay with distance, as was expected, and it was not possible to maintain a connection over the same range as with 5G. We did, however, note significantly higher speeds from WiFi connections at close proximity:
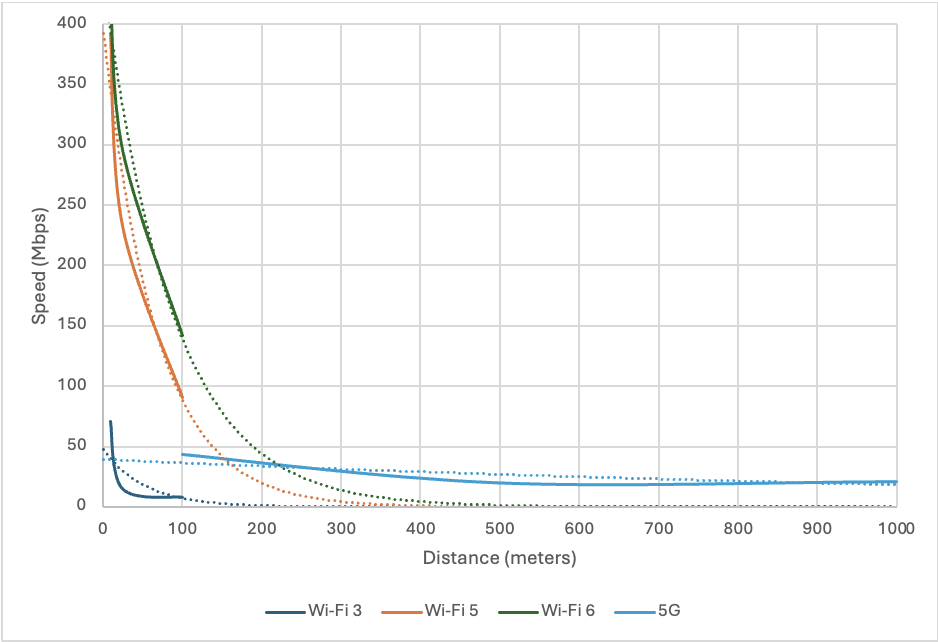
Surprisingly, we did not see significant changes in latency or error rates during our testing.
Conclusions
The following network security spectrum summarizes our findings:
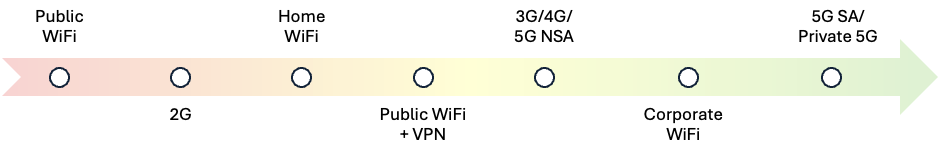
This spectrum provides a high-level overview of network types, from less secure to more secure, based on the characteristics we observed and documented in our whitepaper. The use of layered security mechanisms moves any network towards the more secure end of the spectrum.
Overall, we found that a typical standalone 5G network is more resilient against attacks than a typical WiFi network and that 5G provided a more reliable connection than WiFi, even over significant distances; however, WiFi provided much higher speeds when the wireless device was in close proximity to the wireless access point.
AUTHORS:
– Ethan Shackelford, IOActive Associate Principal Security Consultant
– Vince Marcovecchio, IOActive Senior Security Consultant

